- Cloud Security Newsletter
- Posts
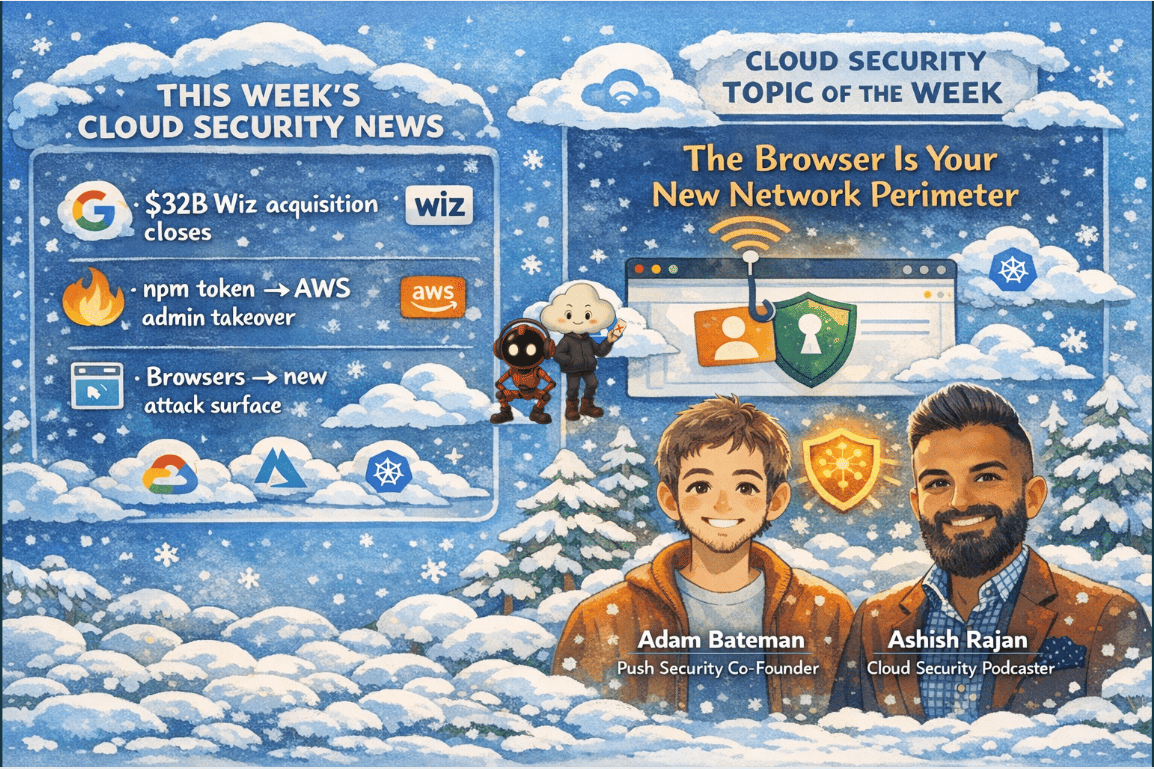
- 🚨 Google Closes $32B Wiz Deal: Why the Browser Is Now Your Biggest Security Blind Spot
🚨 Google Closes $32B Wiz Deal: Why the Browser Is Now Your Biggest Security Blind Spot
This week Google's landmark $32B acquisition of Wiz reshapes cloud security, while a new coalition of identity-focused threat actors Scattered Lapsis Hunters continues to dominate enterprise breaches through browser-native attacks. Push Security co-founder Adam Bateman explains why your IDP is not a firewall, how phishing has moved far beyond the inbox, and why the browser is now the most under-protected attack surface in the enterprise. Keywords: browser security, identity attacks, cloud security M&A, supply chain risk, SaaS phishing, consent phishing, Click Fix.
Hello from the Cloud-verse!
This week’s Cloud Security Newsletter topic: When AI Plays Both Sides: Rethinking SOC Architecture in the Era of 29-Minute Breakouts (continue reading)
Incase, this is your 1st Cloud Security Newsletter! You are in good company!
You are reading this issue along with your friends and colleagues from companies like Netflix, Citi, JP Morgan, Linkedin, Reddit, Github, Gitlab, CapitalOne, Robinhood, HSBC, British Airways, Airbnb, Block, Booking Inc & more who subscribe to this newsletter, who like you want to learn what’s new with Cloud Security each week from their industry peers like many others who listen to Cloud Security Podcast & AI Security Podcast every week.
Welcome to this week’s Cloud Security Newsletter
If you had to pick one thread connecting every major enterprise breach of the last 18 months, it wouldn't be a zero-day or a misconfigured S3 bucket. It would be identity compromised through the browser.
This week's edition comes at a pivotal moment. Google's $32 billion Wiz acquisition, the largest cybersecurity deal in history, is closed. A coalition of identity-focused threat actors is now operating under a single banner (Scattered Lapsis Hunters), having already compromised MGM, Okta, Marks & Spencer, and Salesforce. And the attack vector enabling all of it? The browser is a surface that most enterprise security programs still treat as someone else's problem.
To make sense of this shift, we spoke with Adam Bateman, co-founder of Push Security and former elite red teamer at MWR whose simulations were so convincing they were mistaken for real nation-state attacks and appeared in public threat intelligence reports. Adam brings a decade of offensive security research to the question of why identity controls are failing and what defenders actually need to do about it. [Listen to the episode]
⚡ ONE STAT THAT MATTERS
72 hours
The time it took threat actor UNC6426 to escalate from a stolen developer token to full AWS administrative control — without exploiting a single infrastructure vulnerability. Identity trust chains are now the primary blast radius multiplier in cloud breaches.
⚡ TL;DR for Busy Readers
Google closes $32B Wiz acquisition
Expect tighter CNAPP + threat intelligence integration and potential licensing shifts.Scattered Lapsis Hunters coalition emerges
Identity-focused actors combining tactics from Scattered Spider, Lapsus$, and ShinyHunters.Supply chain breach → AWS admin in 72 hours
GitHub OIDC trust abuse enabled full environment takeover.Audit your GitHub-to-AWS OIDC trust policies today
Identity providers ≠ security boundaries
40%+ of SaaS apps remain invisible to most conditional access policies.Browser security becomes the new EDR frontier
Modern phishing now executes entirely inside the browser.
📰 THIS WEEK'S TOP 6 SECURITY HEADLINES
Each story includes why it matters and what to do next — no vendor fluff.
1. 🚨 MAJOR M&A Google Closes $32B Wiz Acquisition
What Happened: Google completed its $32 billion all-cash acquisition of Wiz. The deal passed U.S. antitrust review in November 2025 and received unconditional EU approval in February 2026. The combined platform merges Google's Threat Intelligence and Security Operations with Wiz's CNAPP/CSPM. Critically, Wiz remains available across AWS, Azure, and Oracle Cloud.
Why It Matters: The consolidation of Mandiant (IR + threat intel) with Wiz (CNAPP/CSPM) creates a formidable platform and immediate pressure on Palo Alto Networks and Microsoft Defender for Cloud. For teams currently on Wiz: integration roadmap, commercial terms, and Gemini AI integration pace deserve scrutiny over the next 12 months.
Sources: Google Cloud Blog | SecurityWeek | TechCrunch | Wiz Blog
2. 🚨 SUPPLY CHAIN Stolen npm Token Gives Attacker Full AWS Admin in 72 Hours
What Happened: Threat actor UNC6426 leveraged a developer's GitHub token stolen via the nx npm package supply chain compromise to achieve full cloud environment takeover in under 72 hours. The attacker abused the GitHub-to-AWS OIDC trust relationship to create a new administrator role, exfiltrated Amazon S3 data, performed production data destruction, and publicly renamed all internal GitHub repositories.
Why It Matters: Any IAM role whose trust policy references token.actions.githubusercontent.com without a StringEquals condition on the sub claim is exploitable today. Audit GitHub-to-AWS OIDC trust configurations immediately and treat overly permissive IAM roles as critical misconfigurations not policy aspirations.
Sources: The Hacker News | CSA Research Brief
3. 🔍 CLOUD VULN "LeakyLooker": Nine Cross-Tenant Flaws in Google Looker Studio
What Happened: Tenable Research disclosed nine cross-tenant vulnerabilities in Google Looker Studio enabling arbitrary SQL queries against BigQuery, Google Sheets, Spanner, PostgreSQL, MySQL, and Cloud Storage. A key flaw: duplicated reports retained stored database credentials, letting the new report owner run custom SQL without knowing the password. Google has patched all issues.
Why It Matters: Analytics and BI platforms connected to sensitive cloud databases are a seriously underappreciated attack surface. The credential-inheritance flaw illustrates how feature convenience ("copy this report") becomes a security liability at scale. Review access controls on shared Looker Studio reports and audit who can duplicate data-connected dashboards.
Sources: Tenable Research | The Hacker News | Infosecurity Magazine
4. 🚨 EMERGING VECTOR Malicious Rust Crates and AI-Powered CI/CD Bots Target Developer Secrets
What Happened: Researchers discovered five malicious Rust crates on crates.io (late February – early March 2026) disguised as time utilities, covertly exfiltrating .env file data. Simultaneously, an AI-powered bot named "hackerbot-claw" scanned public repositories for exploitable GitHub Actions workflows, targeting secrets at Microsoft, Datadog, and Aqua Security. In the Aqua incident, attackers pushed malicious Trivy VS Code extensions and used local AI coding agents to exfiltrate data.
Why It Matters: .env files frequently contain cloud provider API keys, database credentials, and GitHub tokens. Mandate cargo-audit and cargo-deny in all Rust-based CI pipelines. Audit GitHub Actions workflows for pull_request_target exposure. Treat AI coding agents on developer machines as a monitored security boundary.
Sources: The Hacker News | Socket Research
5. ⚠️ AI SECURITY OpenAI Acquires Promptfoo, Bringing AI Red-Teaming into the Core Platform
What Happened: OpenAI announced plans to acquire Promptfoo, an AI security platform for identifying and remediating vulnerabilities in AI systems. The technology integrates into OpenAI Frontier for enterprise AI agent security testing and monitoring. The open-source project continues.
Why It Matters: Agent security testing red-teaming, indirect prompt injection, safety evals is moving from niche AppSec work into core platform capability. Deploying AI agents without built-in red-teaming infrastructure will become a compliance gap, not just a best-practice shortfall.
6. ⚠️ SAAS RISK Salesforce Warns of Active Data-Harvesting Against Experience Cloud Sites
What Happened: Salesforce disclosed a threat actor mass-scanning public-facing Experience Cloud sites using a modified version of Mandiant's AuraInspector to exploit overly permissive guest-user settings. ShinyHunters part of the Scattered Lapsis Hunters coalition has publicly claimed responsibility.
Why It Matters: SaaS risk most often sits in authorization design, not software defects. Immediate actions: review guest-user profiles, set external access defaults to private, disable unauthenticated public API access, and inspect Aura event logs for unusual query patterns.
🎯 Cloud Security Topic of the Week:
The Browser Is Your New Network Perimeter
For most of security's history, the network was the thing you defended. EDR extended that logic to the endpoint. But there is now a third layer one that most enterprise security programs have left almost entirely unprotected: the browser.
The architectural shift is already complete. Employees work inside browsers, not applications. They talk to cloud services, not internal networks. Identity not network access is the control plane. And yet almost no organisation has deployed the equivalent of EDR for the browser. That gap is exactly what groups like Scattered Lapsis Hunters are exploiting and it's why every major enterprise breach of the past 18 months started not with a firewall bypass, but with an identity compromise that detonated entirely inside the browser.
This week, Adam Bateman of Push Security walked through exactly how this shift has happened, what attack patterns are dominating, and why the existing stack IDPs, MFA, SWGs, even EDR has a structural blind spot that only browser-native visibility can close.
Featured Experts This Week 🎤
Adam Bateman - Co-Founder & CEO | Push Security
Ashish Rajan - CISO | Co-Host AI Security Podcast , Host of Cloud Security Podcast
Definitions and Core Concepts 📚
Before diving into our insights, let's clarify some key terms:
IDP (Identity Provider): A centralised platform (e.g., Okta, Entra ID) that manages authentication across applications. Adam's key point: IDPs function more like domain controllers than firewalls they provide a management layer, but attackers bypass them by targeting local accounts or SaaS apps users access outside SSO flows.
OIDC (OpenID Connect): An authentication protocol built on OAuth 2.0. The GitHub-to-AWS OIDC trust is a common CI/CD pattern but without a StringEquals condition on the sub claim, any attacker with a GitHub token can assume privileged IAM roles.
Click Fix Attack: A social engineering technique that injects a malicious command into the user's clipboard via JavaScript. The user is prompted to paste and execute via Windows Run downloading malware. EDR often misses it because the command runs as a direct user action, not a suspicious process chain.
Consent Fix Attack: Push Security's newly named variant combining Click Fix with OAuth consent phishing, attributed to Midnight Blizzard. The user is tricked into performing actions granting an attacker full Azure control entirely inside the browser, with zero code executed on the endpoint.
Consent Phishing : An attack tricking users into granting OAuth permissions to a malicious application. The attacker then controls it via API, accessing email and files and performing password resets bypassing MFA entirely by using a legitimate token rather than logging in.
Omni-channel Phishing : The evolution of credential phishing beyond email. Attackers now deliver phishing links through LinkedIn DMs, SMS, social media comments, Google Ads sponsored results, and personal email inboxes all detonating inside the browser.
Scattered Lapsis Hunters: The newly-formed coalition of Scattered Spider, Lapsus$, and ShinyHunters collectively responsible for breaches at MGM, Okta, Microsoft, JLR, Marks & Spencer, and Salesforce. Their MO is purely identity-first; none of their major breaches started on the network.
Secure Web Gateway (SWG): A proxy-based solution for monitoring web traffic via SSL interception. Adam's analysis: modern JavaScript-heavy SaaS apps stage their payloads client-side meaning the SWG never sees the full application. Browser-native tools have the full runtime context the SWG never will.
CNAPP: Cloud-Native Application Protection Platform an integrated platform combining CSPM, workload protection, network security, and IaC scanning. Wiz is the defining product in this category, now integrated with Google's Mandiant threat intelligence and Security Operations.
This week's issue is sponsored by Push Security
Learn how browser-based attacks have evolved — get the 2026 report
Most breaches today start with an attacker targeting cloud and SaaS apps directly over the internet. In most cases, there’s no malware or exploits. Attackers are abusing legitimate functionality, dumping sensitive data, and holding companies to ransom. This is now the standard playbook.
The common thread? It's all happening in the browser.
Get the latest report from Push Security to understand how browser-based attacks work, and where they’ve been used in the wild, breaking down AitM attacks, ClickFix, malicious extensions, OAuth consent attacks, and more.
💡Our Insights from this Practitioner 🔍
1. The IDP Is Not a Firewall And Attackers Know It
The central misconception Adam targets is the assumption that deploying Okta or Entra ID creates a security perimeter analogous to a firewall. It doesn't. It creates a management layer and like every management layer, it can be bypassed.
"People take their IDP, whether it be Okta, Entra, whatever it might be, and they say: yeah, it's this with a hundred SaaS applications behind it and everything's got MFA on it. When you actually dig into it... it's not a firewall, it's an overarching management layer. If you gained access to Okta, you could compromise everything beneath it but you can also get into those underlying apps in lots of other ways as well."
The practical mechanism: when users encounter an application login page, they often bypass SSO entirely by clicking "Sign in with Google" or creating a local account outside the IDP. Adam's data shows this happening across thousands of applications, including services like Zapier that can be weaponised to send internal Slack messages once compromised.
What this means for your architecture:
Your IDP policy is only as effective as your enforcement coverage. 40%+ of SaaS apps in most organisations are shadow IT, invisible to your IDP.
Credential stuffing attacks bypass IDP entirely. Attackers don't need to defeat MFA if they can log in with a local credential that was never federated.
OAuth and consent-phishing attacks bypass MFA regardless of strength including hardware keys and passkeys.
2. The Architectural Shift Most Security Teams Haven't Accounted For
The shift Adam describes is structural, not incremental. In the legacy model, the attack surface was open ports. In the modern model, applications live in the cloud; identity is the only path to them. And identity lives in the browser.
"We used to work on our laptops with applications talking to the network. And now we work inside our browsers with our browsers talking to the cloud. The laptop to the network was bound together with ports and protocols. The browser to cloud is bound together with identity. So the modern attacks are now: how do I get access to this identity in a creative way to get access to the cloud services where all the critical data is?" - Adam Bateman
This is why groups like Scattered Lapsis Hunters are so effective. They're not finding novel exploits, they're applying sound offensive logic to an architecture most defenders are still protecting with the wrong tools. Even organisations that are 50% on-premise have a cloud and SaaS footprint that represents an uncovered attack surface. It's not a transition problem, it's a permanent gap without browser-level visibility.
3. Phishing Has Outgrown the Inbox
Two distinct evolutions of phishing that bypass both traditional email security and endpoint detection entirely:
Omni-channel Phishing
Push Security has documented campaigns where attackers compromised LinkedIn accounts and used them to DM phishing links to high-profile CEOs from a known, trusted contact. The corporate email gateway saw nothing. Adam's team has also observed delivery via SMS, social media comments, and legitimate SaaS apps including DocuSign documents with embedded phishing links and Google Ads-distributed phishing via sponsored results.
Legitimate SaaS as a Phishing Vehicle
Traditional email security works by identifying illegitimate sending domains. Attackers have neutralised that control by sending phishing from legitimate SaaS platforms. A $20 DocuSign account, a real-looking court order with a large signing button and the email arrives from docusign.com, which is legitimate. The phish happens when the user opens the browser to sign.
Click Fix & Consent Fix: Browser-Native Payload Chains
Click Fix (clipboard injection → user pastes and executes) is now prolific. The Consent Fix variant attributed to Midnight Blizzard is the most technically significant development: a user hits a watering-hole site, performs browser actions, and the result is a full Azure compromise. No PowerShell. No endpoint execution. No EDR alert.
"Email is no longer the target anymore. Phishing has evolved to a lot more things happening inside the browser." - Ashish
4. What Browser Security Actually Looks Like And Who Owns It
The ownership question for browser security is unresolved in most enterprises. IT owns browser deployment. But browser security detection and response for identity compromise, phishing, malicious extensions, session hijacking belongs to no one.
Push Security positions itself as detection and response tooling bought by the same team that runs EDR. The mechanism: a browser extension that observes logins across all SaaS applications including shadow IT, inspects the DOM, profiles login pages, and detects cloned phishing pages. Because it covers every identity event across every app (not just IDP-managed ones), it closes the gap SSPM tools can't reach via API alone.
The longer-term category play: the displacement of Secure Web Gateways. The same evolutionary logic that transformed AV → EDR is now playing out with SWG → Browser Security.
Practical steps for security architects:
Map your SaaS footprint honestly including shadow IT. 40%+ of SaaS apps are unmanaged. You cannot secure what you cannot see.
Audit your IDP coverage. Identify every application where users can log in without SSO and either enforce federated identity or accept and monitor the risk.
Review OAuth app permissions across M365 and Google Workspace for apps with Mail.Read, Mail.Send, or Files.ReadWrite granted by individual users.
Add browser security to your stack evaluation Push Security, enterprise browser tooling, or managed browser solutions.
Assign ownership. SOC, identity team, or cloud security someone needs to own this explicitly, or it will remain unowned.
✅ WHAT SECURITY LEADERS SHOULD DO THIS WEEK
Audit GitHub-to-AWS OIDC roles for missing sub claim restrictions the misconfiguration that enabled the 72-hour AWS takeover.
Review SaaS analytics access controls for dashboards connected to production databases, particularly duplication and sharing permissions.
Add dependency-scanning to Rust pipelines using cargo-audit and cargo-deny to detect malicious crates.
Audit Salesforce Experience Cloud guest user profiles to ensure anonymous users cannot access internal objects or APIs.
Map your full SaaS footprint including shadow IT and assign explicit ownership of browser-based identity threat detection.
🧠 MENTAL MODEL OF THE WEEK
The Trust Chain Model
Developer Workstation → SaaS Platform → CI/CD Pipeline → Cloud IAM Role
Cloud compromises rarely start with infrastructure exploitation. They begin by breaking the weakest trust relationship in the identity chain. The attacker only needs one weak link to inherit the privileges of the entire chain. Map every trust relationship in your developer ecosystem not just your cloud environment.
Push Security Research Blog — Click Fix, Consent Fix, and Omnichannel Phishing
Google Cloud Threat Horizons Report H1 2026 — Supply chain and OIDC trust analysis
Tenable LeakyLooker Research — Cross-tenant flaws in cloud analytics platforms
OWASP OAuth Security Cheatsheet — Consent phishing and OAuth app risks
Socket Research — Malicious Rust crates and supply chain detection
Cloud Security Podcast

Question for you? (Reply to this email)
🤔 Does your security team have explicit ownership of browser-based identity threats or is the browser still a gap between IT, SOC, and identity?
Next week, we'll explore another critical aspect of cloud security. Stay tuned!
📬 Want weekly expert takes on AI & Cloud Security? [Subscribe here]”
We would love to hear from you📢 for a feature or topic request or if you would like to sponsor an edition of Cloud Security Newsletter.
Thank you for continuing to subscribe and Welcome to the new members in tis newsletter community💙
Peace!
Was this forwarded to you? You can Sign up here, to join our growing readership.
Want to sponsor the next newsletter edition! Lets make it happen
Have you joined our FREE Monthly Cloud Security Bootcamp yet?
checkout our sister podcast AI Security Podcast